-
 Bitcoin
Bitcoin $109,459.7682
2.44% -
 Ethereum
Ethereum $2,598.6052
6.29% -
 Tether USDt
Tether USDt $1.0003
0.00% -
 XRP
XRP $2.2734
3.95% -
 BNB
BNB $661.4886
1.58% -
 Solana
Solana $155.4825
4.35% -
 USDC
USDC $0.9999
-0.02% -
 TRON
TRON $0.2838
1.04% -
 Dogecoin
Dogecoin $0.1740
8.25% -
 Cardano
Cardano $0.6047
9.04% -
 Hyperliquid
Hyperliquid $40.2302
6.50% -
 Sui
Sui $2.9863
10.05% -
 Bitcoin Cash
Bitcoin Cash $509.5786
0.60% -
 Chainlink
Chainlink $13.8156
6.03% -
 UNUS SED LEO
UNUS SED LEO $9.0142
0.69% -
 Avalanche
Avalanche $19.0337
8.68% -
 Stellar
Stellar $0.2438
5.17% -
 Toncoin
Toncoin $2.9012
3.59% -
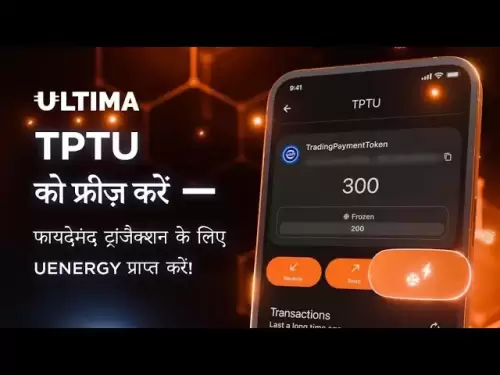
 Shiba Inu
Shiba Inu $0.0...01210
6.20% -
 Litecoin
Litecoin $90.0882
7.05% -
 Hedera
Hedera $0.1597
8.53% -
 Monero
Monero $326.3340
2.88% -
 Polkadot
Polkadot $3.6365
9.32% -
 Bitget Token
Bitget Token $4.6162
2.72% -
 Dai
Dai $1.0001
0.00% -
 Ethena USDe
Ethena USDe $1.0002
-0.01% -
 Uniswap
Uniswap $7.6403
10.47% -
 Pepe
Pepe $0.0...01060
12.03% -
 Aave
Aave $281.3664
7.56% -
 Pi
Pi $0.4992
1.76%
What is public key cryptography?
Public key cryptography uses paired keys (public & private) for secure communication and data integrity, eliminating the need for pre-shared secrets, and is crucial for cryptocurrency functionality and digital signatures.
Mar 16, 2025 at 11:51 pm

Key Points:
- Public key cryptography uses a pair of keys: a public key for encryption and verification, and a private key for decryption and signing.
- It ensures secure communication and data integrity even without pre-shared secrets.
- Asymmetric encryption, the foundation of public key cryptography, is crucial for various cryptocurrency functionalities.
- Understanding the mathematical principles behind public key cryptography is essential for comprehending its security and applications in blockchain technology.
- Different algorithms, like RSA and ECC, underpin various public key cryptographic systems.
What is Public Key Cryptography?
Public key cryptography, also known as asymmetric cryptography, is a cornerstone of modern secure communication, especially within the cryptocurrency realm. Unlike symmetric cryptography which uses a single secret key for both encryption and decryption, public key cryptography employs a pair of mathematically linked keys: a public key and a private key. The public key, as its name suggests, can be freely shared, while the private key must be kept absolutely secret.
This seemingly simple distinction has profound implications for security and usability. The public key is used to encrypt messages intended for the owner of the corresponding private key. Only the private key holder can decrypt the message using their secret key. This eliminates the need for pre-shared secret keys, a significant advantage in distributed and decentralized systems like cryptocurrencies.
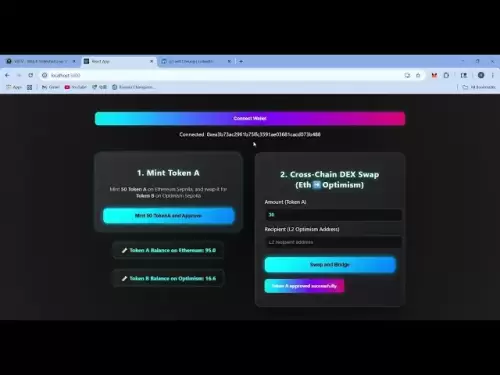
How Does Public Key Cryptography Work?
The magic behind public key cryptography lies in its underlying mathematical functions. These functions are designed such that it's computationally easy to encrypt a message using the public key but computationally infeasible to decrypt it without the corresponding private key. The strength of the system rests on the difficulty of deriving the private key from the public key. This computational asymmetry is the core of its security.
The process typically involves two main operations: encryption and decryption. Encryption uses the recipient's public key to transform the plaintext message into an unreadable ciphertext. Decryption, on the other hand, uses the recipient's private key to reverse the process and recover the original plaintext message. The mathematical functions used vary depending on the specific public key cryptographic algorithm.
Public Key Cryptography in Cryptocurrencies:
Public key cryptography plays a vital role in various aspects of cryptocurrency functionality. Let's explore some key applications:
- Digital Signatures: Cryptocurrencies use digital signatures to verify the authenticity and integrity of transactions. A user signs a transaction using their private key, creating a digital signature. Anyone can then verify the signature using the sender's public key, confirming the transaction's origin and preventing tampering.
- Secure Communication: Public key cryptography enables secure communication between users and nodes in a cryptocurrency network. Users can encrypt messages using the recipient's public key, ensuring only the intended recipient can read the message. This is crucial for maintaining privacy and preventing eavesdropping.
- Wallet Security: Cryptocurrency wallets utilize public key cryptography to secure users' funds. Each wallet has a pair of keys: a public key for receiving funds and a private key for authorizing transactions. The private key must be kept secret to prevent unauthorized access to the wallet.
Common Public Key Cryptographic Algorithms:
Several algorithms underpin public key cryptography systems. Two prominent examples include:
- RSA (Rivest–Shamir–Adleman): RSA is one of the oldest and most widely used public key algorithms. Its security relies on the difficulty of factoring large numbers.
- Elliptic Curve Cryptography (ECC): ECC offers comparable security to RSA with smaller key sizes, making it more efficient for resource-constrained devices. It's increasingly favored in cryptocurrencies due to its efficiency.
Understanding the Mathematical Foundation:
While the details can be complex, understanding the underlying mathematical principles is crucial for appreciating the security of public key cryptography. The algorithms are built on mathematical problems that are considered computationally hard to solve. These problems, such as factoring large numbers (in RSA) or solving the elliptic curve discrete logarithm problem (in ECC), provide the foundation for the system's security. The strength of the cryptography directly correlates to the difficulty of solving these underlying mathematical problems. Advances in computing power and the development of new algorithms constantly challenge the security of these systems, prompting ongoing research and development of more robust algorithms.
The implementation of these algorithms involves intricate mathematical operations that transform data in a way that is only reversible with the correct key. The security relies on the secrecy of the private key and the computational infeasibility of deriving it from the public key.
Frequently Asked Questions:
Q: What is the difference between public and private keys?
A: The public key is like your address – you can share it freely with anyone. The private key is like your secret password – you must keep it absolutely confidential. The public key is used to encrypt messages sent to you, and your private key decrypts them.
Q: How secure is public key cryptography?
A: The security of public key cryptography depends on the strength of the underlying mathematical algorithms and the length of the keys used. Longer keys generally provide stronger security. However, advances in computing power and the development of new algorithms could potentially weaken the security of existing systems. Therefore, regular updates and the adoption of newer, more secure algorithms are crucial.
Q: Can public key cryptography be broken?
A: Theoretically, yes, with sufficient computing power. However, for currently used key sizes and algorithms, breaking public key cryptography is computationally infeasible with today's technology. The security relies on the assumption that breaking the underlying mathematical problem is computationally intractable.
Q: What are some real-world applications of public key cryptography beyond cryptocurrencies?
A: Public key cryptography is used extensively in securing online communications (HTTPS), digital signatures for software verification, and secure email systems, among other applications. Its ability to secure communication without pre-shared secrets makes it indispensable in many aspects of modern technology.
Q: How are public and private keys generated?
A: Key generation involves complex mathematical processes specific to the chosen algorithm (RSA, ECC, etc.). Cryptographic libraries and tools handle this process, ensuring the keys are properly generated and the private key is kept secure. The details of these generation processes are generally not exposed to the end-user. They are handled behind the scenes by the software or hardware used.
Disclaimer:info@kdj.com
The information provided is not trading advice. kdj.com does not assume any responsibility for any investments made based on the information provided in this article. Cryptocurrencies are highly volatile and it is highly recommended that you invest with caution after thorough research!
If you believe that the content used on this website infringes your copyright, please contact us immediately (info@kdj.com) and we will delete it promptly.
- Eurau Stablecoin: Deutsche Bank, Galaxy, and Bafin Approval Usher in New Era
- 2025-07-03 20:30:12
- Solana DEX Volume and Ranking: Riding the Wave to the Top
- 2025-07-03 21:10:20
- BONK ETF Buzz: News, Catalysts, and What's Driving the Meme Coin Mania
- 2025-07-03 21:10:20
- Stablecoin Market: JPM's Forecast vs. Trillion-Dollar Potential—Reality Check?
- 2025-07-03 21:50:12
- Kane Brown Trades Country for Comedy: A Rom-Com Debut!
- 2025-07-03 21:50:12
- Check Your Change! That 1p Coin Could Be Worth £200k!
- 2025-07-03 21:20:17
Related knowledge

How to cancel a pending transaction in Phantom wallet?
Jul 03,2025 at 07:21pm
Understanding Pending Transactions in Phantom WalletA pending transaction in the Phantom wallet occurs when a user initiates a transfer or interaction with the Solana blockchain, but it hasn't yet been confirmed by the network. This can happen due to various reasons such as low transaction fees, network congestion, or incorrect gas settings. It's import...

How to lock my Phantom wallet extension?
Jul 03,2025 at 11:14am
What Is the Phantom Wallet and Why Lock It?The Phantom wallet is a popular non-custodial cryptocurrency wallet designed for interacting with the Solana blockchain. Supporting both browser extensions and mobile apps, Phantom allows users to store, send, receive, and stake SOL tokens, as well as interact with decentralized applications (dApps). Securing y...

Does Phantom wallet offer two-factor authentication (2FA)?
Jul 03,2025 at 09:00am
Understanding Phantom Wallet and Its Security FeaturesPhantom wallet is a widely used non-custodial cryptocurrency wallet that supports the Solana blockchain. It allows users to store, send, receive, and interact with decentralized applications (dApps) seamlessly. As security is a top priority for any crypto wallet user, security features like two-facto...
What is "rent" on Solana and how does it affect my Phantom wallet?
Jul 02,2025 at 08:35pm
Understanding 'Rent' on SolanaIn the context of Solana, the term 'rent' refers to a storage fee that users pay for maintaining data on the blockchain. Unlike Ethereum, where storage costs are paid once via gas fees during contract deployment, Solana implements a recurring cost model to ensure efficient usage of network resources. This means that any acc...

Is Phantom wallet open source?
Jul 03,2025 at 12:29am
What is Phantom Wallet?Phantom wallet is a non-custodial cryptocurrency wallet primarily designed for the Solana blockchain. It allows users to store, send, receive, and interact with decentralized applications (dApps) on the Solana network. The wallet is available as a browser extension and mobile application, offering a seamless experience for both be...

Why is my Phantom wallet app crashing?
Jul 02,2025 at 07:35pm
Understanding Phantom Wallet App CrashesIf you're experiencing issues with the Phantom wallet app crashing, you're not alone. Many users have reported similar problems, especially during high network activity or after recent updates. Phantom is a popular Solana-based wallet that allows users to store, send, and receive SOL tokens as well as interact wit...

How to cancel a pending transaction in Phantom wallet?
Jul 03,2025 at 07:21pm
Understanding Pending Transactions in Phantom WalletA pending transaction in the Phantom wallet occurs when a user initiates a transfer or interaction with the Solana blockchain, but it hasn't yet been confirmed by the network. This can happen due to various reasons such as low transaction fees, network congestion, or incorrect gas settings. It's import...

How to lock my Phantom wallet extension?
Jul 03,2025 at 11:14am
What Is the Phantom Wallet and Why Lock It?The Phantom wallet is a popular non-custodial cryptocurrency wallet designed for interacting with the Solana blockchain. Supporting both browser extensions and mobile apps, Phantom allows users to store, send, receive, and stake SOL tokens, as well as interact with decentralized applications (dApps). Securing y...

Does Phantom wallet offer two-factor authentication (2FA)?
Jul 03,2025 at 09:00am
Understanding Phantom Wallet and Its Security FeaturesPhantom wallet is a widely used non-custodial cryptocurrency wallet that supports the Solana blockchain. It allows users to store, send, receive, and interact with decentralized applications (dApps) seamlessly. As security is a top priority for any crypto wallet user, security features like two-facto...
What is "rent" on Solana and how does it affect my Phantom wallet?
Jul 02,2025 at 08:35pm
Understanding 'Rent' on SolanaIn the context of Solana, the term 'rent' refers to a storage fee that users pay for maintaining data on the blockchain. Unlike Ethereum, where storage costs are paid once via gas fees during contract deployment, Solana implements a recurring cost model to ensure efficient usage of network resources. This means that any acc...

Is Phantom wallet open source?
Jul 03,2025 at 12:29am
What is Phantom Wallet?Phantom wallet is a non-custodial cryptocurrency wallet primarily designed for the Solana blockchain. It allows users to store, send, receive, and interact with decentralized applications (dApps) on the Solana network. The wallet is available as a browser extension and mobile application, offering a seamless experience for both be...

Why is my Phantom wallet app crashing?
Jul 02,2025 at 07:35pm
Understanding Phantom Wallet App CrashesIf you're experiencing issues with the Phantom wallet app crashing, you're not alone. Many users have reported similar problems, especially during high network activity or after recent updates. Phantom is a popular Solana-based wallet that allows users to store, send, and receive SOL tokens as well as interact wit...
See all articles